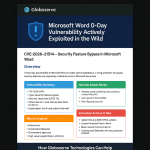
🛡️ Microsoft Word 0‑Day Vulnerability Actively Exploited in the Wild
The Definitive App Password Guide: Simple Steps That Instantly Solve SMTP Issues 2026
New AirSnitch Attack Bypasses Wi‑Fi Encryption in Homes, Offices & Enterprises
A newly‑discovered Wi‑Fi attack technique known as AirSnitch exposes a critical architectural flaw across WPA2, WPA3, guest Wi‑Fi and enterprise deployments — allowing attackers to intercept, manipulate, and re‑route traffic even on supposedly isolated networks.
Breaks Wi‑Fi Encryption
Researchers demonstrated that AirSnitch can bypass client isolation on routers from Netgear, D‑Link, Ubiquiti, Cisco and more — even on WPA3 networks.
Machine‑in‑the‑Middle Capabilities
Attackers can impersonate devices, intercept traffic, steal cookies, perform DNS poisoning, and manipulate data in real‑time.
100% Failure Rate in Tests
Every tested Wi‑Fi network — home routers, enterprise WPA3, multi‑AP systems and public Wi‑Fi — was vulnerable to at least one AirSnitch variant.
What Exactly Is AirSnitch?
AirSnitch is a set of attack primitives that exploit fundamental design flaws in Wi‑Fi’s Layer‑1 and Layer‑2 architecture. It does not break WPA2/WPA3 encryption directly — instead, it bypasses the assumption that encrypted Wi‑Fi clients are isolated from each other.
The attack abuses:
Shared broadcast keys (GTK) that allow malicious packet injection. Inconsistent cross‑layer identity linking allowing MAC/IP spoofing.Single‑layer isolation enforcement leaving gaps at switching or routing boundaries.
This gives attackers the ability to effectively “wiretap the wire” and intercept or manipulate traffic flowing between devices on the same Wi‑Fi network — even across multiple access points or SSIDs.
Who Is at Risk?
AirSnitch affects nearly all modern Wi‑Fi deployments:
Home routers with WPA2/WPA3 security.
Enterprise multi‑AP Wi‑Fi systems using WPA3‑Enterprise.
Guest Wi‑Fi networks that rely on client isolation.
Public Wi‑Fi at airports, hotels & cafés.
Even environments previously assumed “secure” — such as corporate WPA3‑Enterprise networks — were found vulnerable to traffic interception.
How to Protect Your Network from AirSnitch
Use a trusted VPN for all business traffic to ensure end‑to‑end encryption even when Wi‑Fi isolation fails. Segment internal networks — do not rely solely on Wi‑Fi client isolation.Use separate SSIDs + VLANs for guest, IoT, and corporate traffic.Deploy enterprise‑grade firewalls to inspect lateral movement attempts.Enable per‑device authentication (802.1X) instead of shared pre‑shared keys.Regularly update firmware to receive any vendor‑specific mitigations.
Disable “client isolation” reliance as your only security measure; AirSnitch bypasses it.Audit AP configurations for cross‑layer identity consistency.Enforce HTTPS‑only access to reduce plaintext exposure.Use Secure DNS / DNSSEC to reduce poisoning risks.Monitor Wi‑Fi anomalies such as spoofed MACs or routing changes.
How Globoserve Technologies Helps You Stay Protected
Advanced Wi‑Fi Security Architecture
We redesign your wireless network using VLANs, per‑device authentication, and secure segmentation — removing reliance on weak client isolation controls.
Enterprise‑Grade Firewall + IDS Monitoring
Globoserve deploys Ubiquiti, Fortinet or MikroTik security appliances to detect spoofing, lateral movement and AirSnitch‑like traffic anomalies.
Zero‑Trust Guest & IoT Networks
We build isolated guest networks that cannot bridge traffic to business devices, even when Wi‑Fi isolation fails — preventing machine‑in‑the‑middle attacks.
Secure Your Wi‑Fi Infrastructure Today
Don’t wait for an attacker to exploit your Wi‑Fi. Let Globoserve Technologies secure your home, office, hotel, or enterprise network with industry‑leading protections.