Microsoft 365 Account Types Quick Guide
January 21, 2026
New AirSnitch Attack Bypasses Wi‑Fi Encryption in Homes, Offices & Enterprises
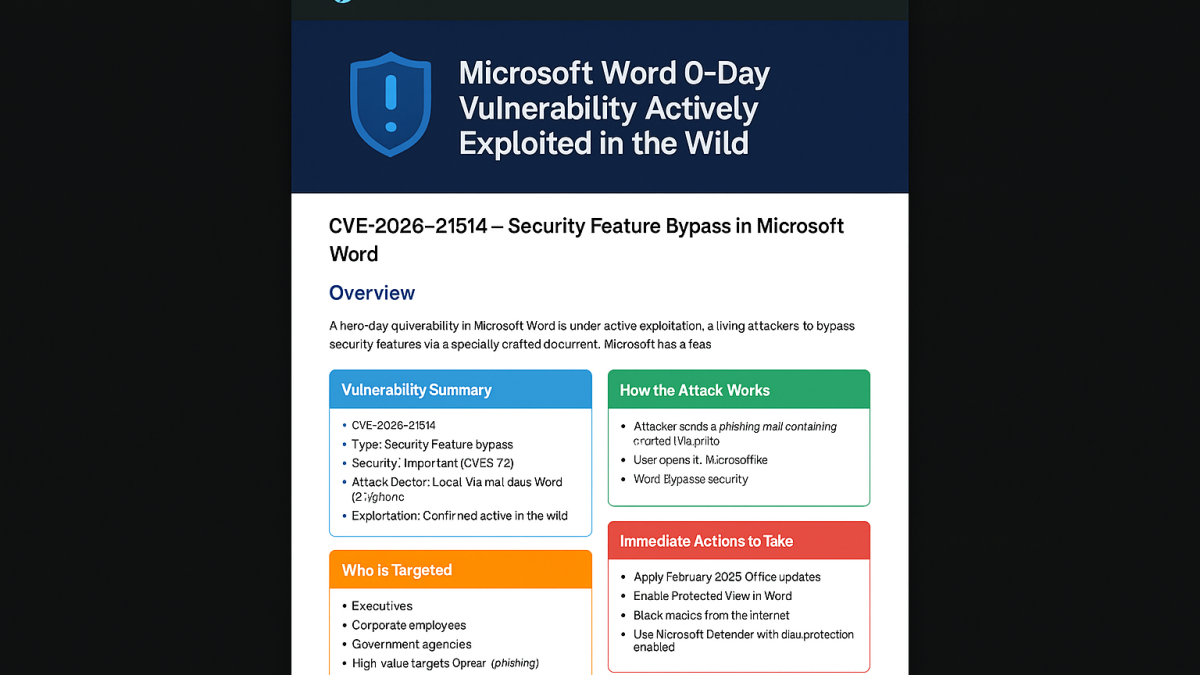
February 27, 2026Vulnerability Summary
- CVE: CVE‑2026‑21514
- Type: Security Feature Bypass
- Severity: CVSS 7.8 (High)
- Exploitation: Confirmed active in the wild
- Attack Vector: Malicious Word document
How the Attack Works
- Attacker sends a phishing email with a crafted Word document.
- User opens the file → security checks are bypassed.
- High‑impact access: data theft, file tampering, system instability.
Who Is Targeted?
- Executives & senior leadership
- Corporate employees
- Government departments
- High‑value targets (spear-phishing)
Immediate Actions to Take
- Apply February 2026 Office updates immediately.
- Enable Protected View in Microsoft Word.
- Block macros from internet sources.
- Deploy Microsoft Defender with cloud protection.
How Globoserve Technologies Helps
Globoserve Technologies provides end-to-end cybersecurity protection for small businesses, hotels, and corporate environments. With the increasing rise of targeted phishing attacks exploiting Microsoft Word 0‑day vulnerabilities, businesses must adopt a stronger security posture.
Our Services Include:
- Patch Management & Automated Updates – we ensure Microsoft Office and Windows machines are always protected and compliant.
- Advanced Email Security & Anti‑Phishing – filter malicious attachments before they reach staff inboxes.
- Endpoint Detection & Response (EDR) – detect and stop zero‑day exploitation attempts in real-time.
- Network Segmentation for Containment – limit data exposure and isolate infected endpoints.
- 24/7 Security Monitoring (SOC) – our team monitors for threats and responds instantly if suspicious activity occurs.
- Staff Cyber Awareness Training – reduce human error, the #1 cause of phishing-driven infections.